Vercel April 2026 Security Incident: Context.ai OAuth Compromise, Exposed Environment Variables, and What Teams Should Do Next
On April 19, 2026, Vercel published a security bulletin about unauthorized access to certain internal systems. (Source: Vercel bulletin) The incident later tied back to a compromise of a third-party AI tool (Context.ai) through a Google Workspace OAuth application. That combination matters because it is not “a Vercel-only problem.” It is a pattern: OAuth + vendor tools + broad scopes can quietly become the shortest path to your production perimeter.
This is a clean brief for engineering leaders and security teams:
- what Vercel confirmed
- what is being reported vs. what is just claimed
- what you should check in the next hour, day, and week
What happened (confirmed)
Vercel’s bulletin states:
- Vercel identified a security incident involving unauthorized access to certain internal systems.
- Vercel engaged incident response experts and notified law enforcement.
- A limited subset of customers was impacted, and Vercel is engaging impacted customers directly.
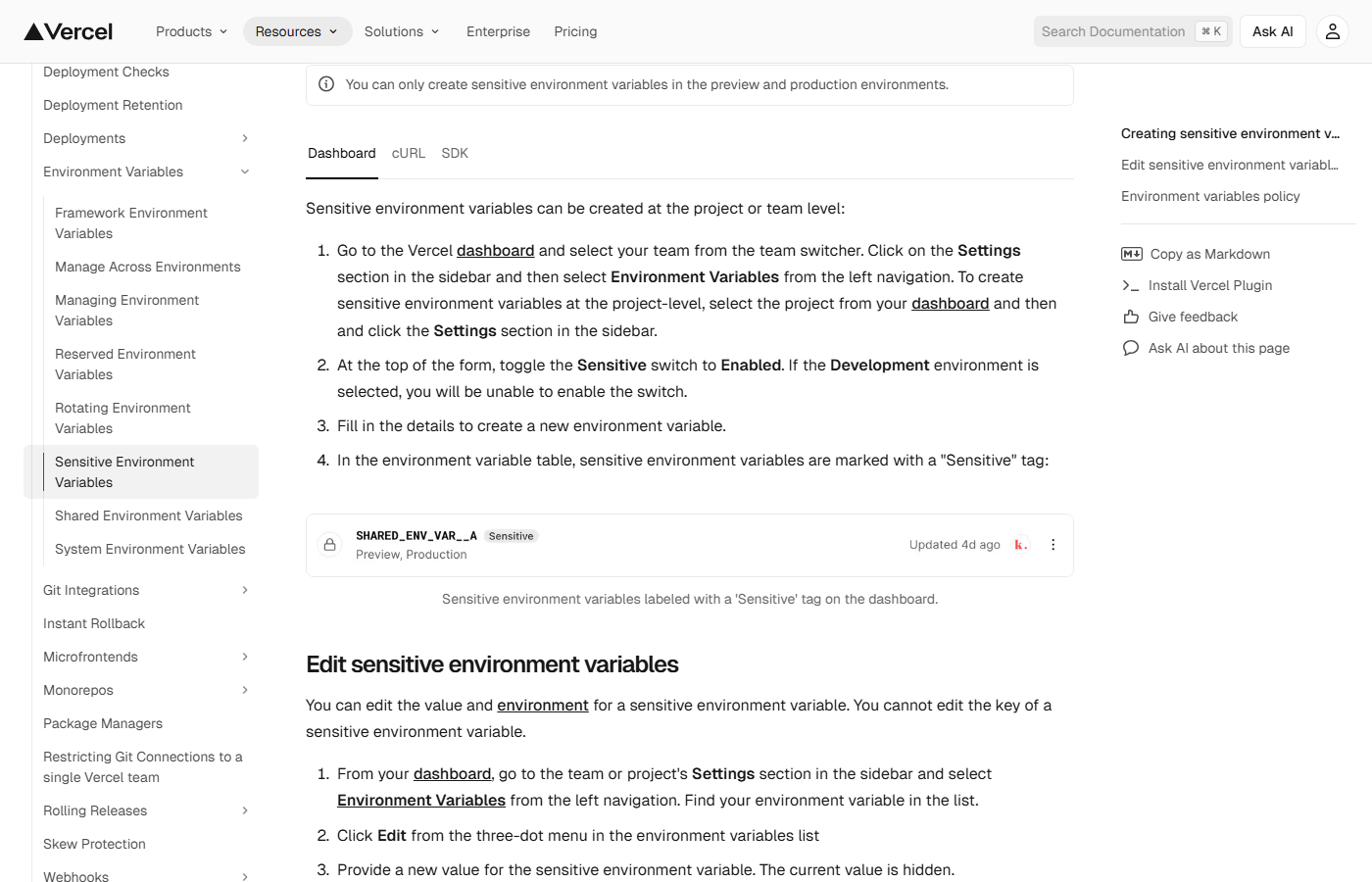
- Vercel recommends customers review environment variables and use the Sensitive Environment Variables feature. (Vercel docs)
Later updates in the same bulletin include an explicit indicator of compromise (IoC): a Google Workspace OAuth app client ID Vercel recommends admins check for immediately.
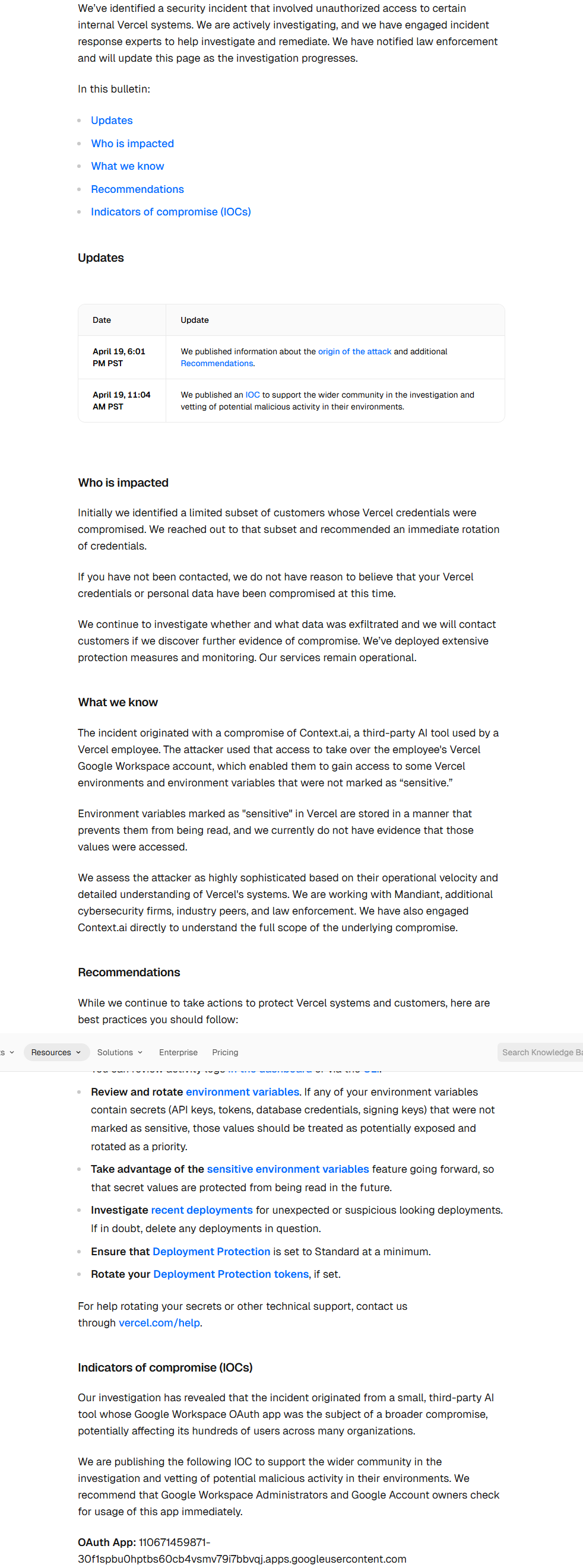
IoC (OAuth app client ID):
110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com
If you are a Google Workspace admin, review the app access controls and investigate whether this client ID appears in your environment. (Google Admin Help)
What could have been exposed (confirmed vs. unknown)
The most operationally important detail in Vercel’s write-up is the distinction between:
- environment variables that were marked Sensitive
- environment variables that were not marked Sensitive
Vercel says that variables marked Sensitive are stored in an unreadable format that prevents them from being read, and it recommends rotating any secrets that were not treated as Sensitive.
What we do not have publicly (at the time of writing, April 20, 2026) is a complete disclosure of the exact customers, projects, and tokens that were accessed. If you run production on Vercel, the practical response is to assume exposure is possible until you have internal evidence that it is not.
Why this incident is bigger than Vercel
This incident highlights a modern reality: the perimeter is often an OAuth grant.
If a third-party tool gets compromised, and it already has an OAuth path into your identity environment, the attacker does not need your password. They need:
- an existing consent grant (or a way to create one)
- enough scope to enumerate useful data
- enough time to pivot before detection
This is also why “shadow AI tools” are not a policy problem. They are an access-control problem.
What is being reported (treat as unverified until confirmed)
There is additional public reporting around this incident, including claims about stolen data and extortion attempts. Treat claims as unverified unless you have direct confirmation from your vendor or internal evidence.
- External coverage: BleepingComputer
Immediate checklist (next hour)
If you use Vercel:
- Rotate anything stored as a non-sensitive environment variable that could act like a secret (API keys, signing keys, DB creds, webhook secrets, OAuth client secrets, third-party tokens).
- Enable Sensitive Environment Variables and re-classify secrets that were misfiled as non-sensitive. (Vercel docs)
- Audit token issuance and privileged sessions tied to build, deploy, and admin actions (Vercel, Git providers, CI, cloud).
If you run Google Workspace:
- Search for and investigate the OAuth app client ID published in Vercel’s bulletin. If it exists in your environment, treat it as a high-signal lead. (Vercel bulletin)
- Revoke third-party app grants you do not explicitly need. (Google Account help)
- Turn on allowlisting / admin approval for OAuth apps so new third-party access cannot appear silently. (Google Admin Help, Google Workspace blog)
Medium-term fixes (next week)
- Treat “non-sensitive env vars” as a design smell. In modern delivery, almost every env var becomes a key at some point.
- Centralize secrets and move them out of build-time convenience stores where possible (secrets manager, KMS-backed flows, short-lived credentials).
- Reduce OAuth blast radius: restrict third-party app access, require admin consent for risky scopes, and continuously review grants.
- Instrument identity: your detection needs to see OAuth grants, token reuse, and unusual access from trusted apps.
A competitive advantage: incident readiness as an engineering habit
The teams that win are not the teams that “never get hit.” They are the teams that:
- notice faster
- scope faster
- rotate faster
- recover without panic
That is a delivery advantage. It protects focus. It protects trust. It keeps the roadmap moving.
If you want a senior-led technical review of your cloud delivery perimeter (OAuth apps, CI/CD trust boundaries, environment variable hygiene, secrets, and incident playbooks), SToFU Systems can help: start with a bounded intervention, leave with a credible next move.
Sources and further reading (reference map)
-
Incident & primary sources
-
Vercel docs worth reviewing
-
Google Workspace controls (OAuth and third-party apps)
-
OAuth risk patterns and overaccess
-
Incident handling references
